In many enterprises, a USB port looks like an ordinary physical interface. In practice, however, it is one of the easiest ways to weaken endpoint control without attracting immediate attention. An employee inserts a personal USB drive into a work laptop to copy a file. A contractor plugs in removable media to deliver materials. Research, finance, HR, and legal endpoints allow general USB devices to connect freely for years. In these situations, the enterprise data boundary is no longer being challenged through sophisticated network attacks. It is being opened directly at the endpoint through a simple hardware connection.
The real difficulty is that enterprises often cannot just shut down all USB usage entirely. Some teams genuinely need approved media. Some temporary projects require offline exchange. Some field-support or delivery scenarios still depend on removable storage. The key question is therefore not whether USB should be completely disabled. It is how to ensure that unauthorized devices cannot connect, while approved and auditable exceptions remain available for legitimate work. That is why USB governance must move beyond simple physical prohibition and become a matter of controlled authorization.
Why unauthorized USB devices remain a high-risk endpoint entry point
The risk of an unauthorized USB device is not limited to copying files out. It matters because it breaks the enterprise’s basic control over endpoint peripheral boundaries. Email monitoring, web upload control, and network-path auditing all assume that data movement can be observed through network channels. Once a USB device is inserted, files can be copied locally and removed directly, bypassing much of that network-focused governance.
There is also a traceability problem. Without a prebuilt authorization mechanism, the enterprise cannot quickly determine whether a certain USB drive was approved by the company, who used it, when it was used, or whether the usage was part of a permitted exception. On the surface, the issue looks like simple device control. Underneath, it is really about unclear device identity, unclear business justification, and unclear operational boundaries.
The goal is not total prohibition, but default control with explicit exceptions
Enterprises usually drift toward one of two extremes in USB management. One is to allow ordinary USB devices to connect freely and rely on audit after something has already happened. The other is to block everything, including legitimate business scenarios that still need removable media. The first leaves the endpoint data boundary open. The second often pushes the business to find workarounds outside the official process, weakening the policy itself.
A more workable model has three layers. First, ordinary USB devices are blocked by default, and only recognized authorized media is allowed. Second, legitimate business exceptions are handled through approval so those cases stay within policy. Third, insertion and usage events are monitored with alerts and audit records, so administrators can control not only whether a device may connect, but also who used it, when, and whether the action was abnormal. That is what turns USB port control from a switch into a real governance process.
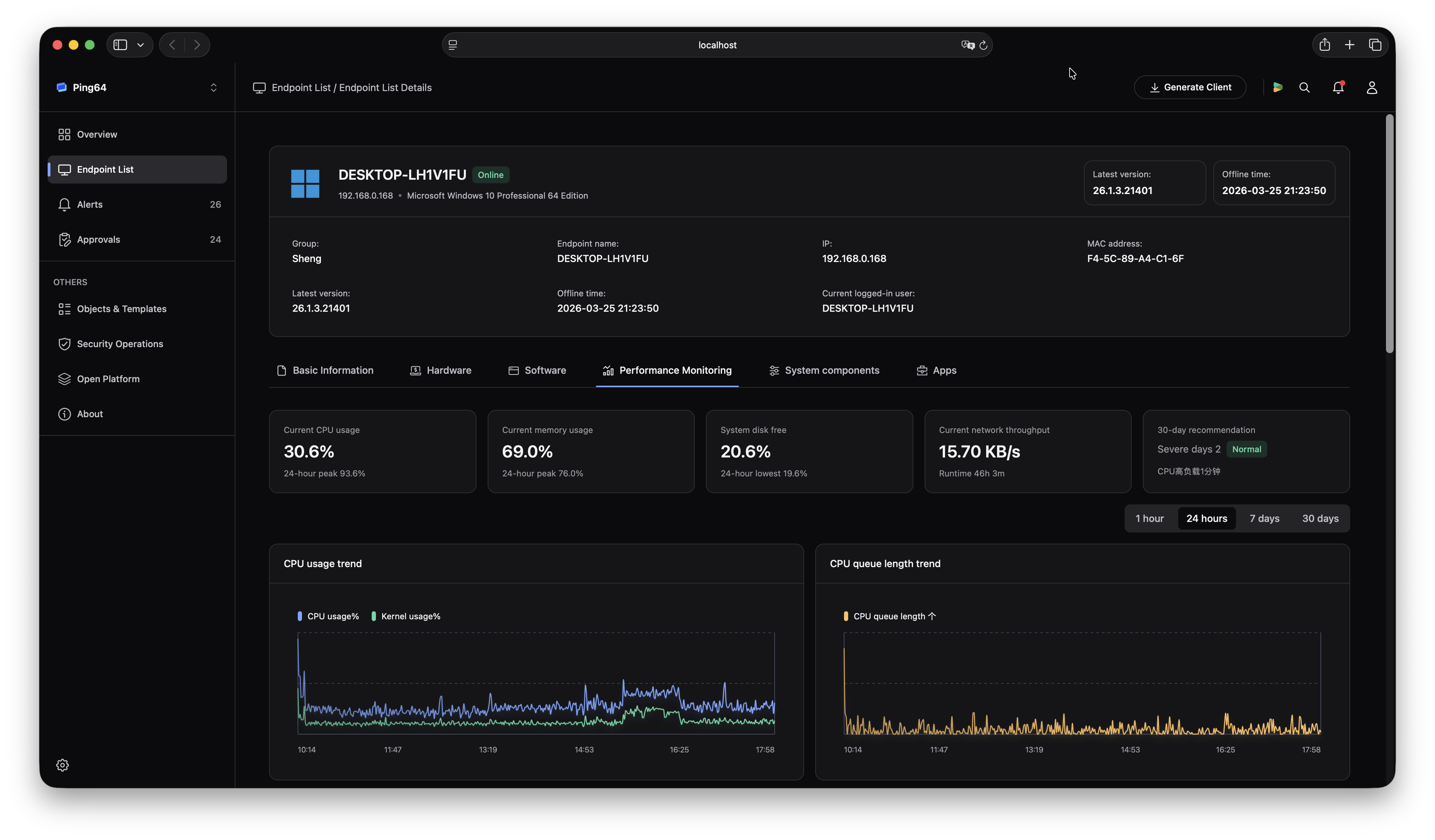
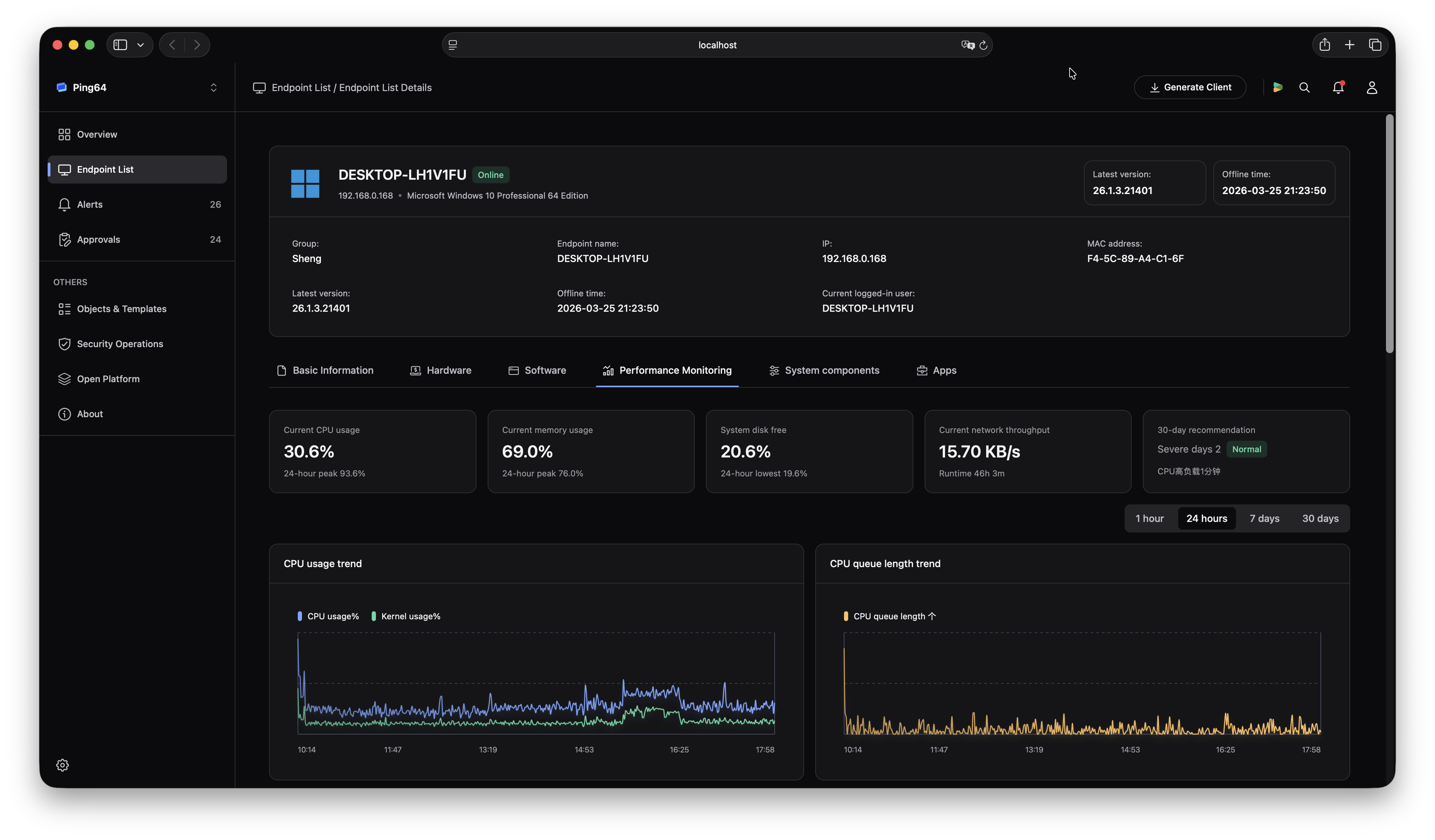
How to use Ping32 to block unauthorized devices from connecting through USB ports
1. Establish the baseline first: ordinary USB blocked, authorized media allowed
Administrators should go to the Device Management module, open Policy, select the endpoints to be controlled, then enter Mobile Storage, enable Permission Settings, and open Parameter Settings. There, general USB drives can be blocked while only authorized drives are allowed for reading. After saving the configuration and applying the policy, the endpoint moves from “any USB device can be used” to “only recognized and approved devices can be used.”
This is the core baseline for USB governance. The value is not simply restricting a port. It is narrowing the range of devices the endpoint is willing to accept. Only after the default state becomes controlled do later authorization, approval, and audit actions have real meaning.
2. Use authorized-drive creation to place legitimate media into a managed allow list
After “block ordinary USB, allow only authorized drives” is enabled, administrators still need to bring legitimate devices into the approved scope. They can do that through Create Authorized Drive in the Device Management module. Ping32 supports three methods: authorize local USB drive, authorize remote USB drive, and offline authorize USB drive. Administrators can choose the proper method depending on where the media is located and whether the target endpoint is online.
This step is not about removing restrictions. It is about giving exception media a clear managed identity. In distributed branches or remote work environments, remote and offline authorization can significantly reduce operational friction. It is also important to note that, according to the manual, formatting an authorized drive cancels its authorization, so authorized media should not be treated as a permanent static list.
3. For necessary business usage, rely on approval instead of permanently opening permissions
If the enterprise has legitimate scenarios such as temporary offline exchange, onsite support, or controlled data delivery, administrators can further enable Allow Usage Approval under Device Management -> Policy -> Mobile Storage -> Permission Settings, then select the relevant approval workflow from the settings icon. In that approval configuration, they can define whether the applicant may request read-only or read-write access and whether the approval duration is chosen by the endpoint user or fixed by the server side.
The purpose here is to keep necessary exceptions inside the formal control model instead of leaving the endpoint permanently open to general USB usage. In stricter environments, it is usually safer to make read-only the default approvable mode and open read-write only when there is a clear business need.
4. Enable USB usage alerts so unauthorized insertion is detected immediately
Permission control alone is not enough. If the enterprise wants to know the moment a USB device is inserted, administrators can go to Device Management -> Policy, select the target endpoints, enter Mobile Storage, enable USB Usage Alert, and inside Parameter Settings check USB Insertion Alert. After the policy takes effect, administrators can review the corresponding events on the Alerts page.
This step moves USB management forward from “review the logs afterward” to “detect unusual insertion immediately.” For sensitive roles such as R&D, finance, HR, and legal, even an attempted unauthorized insertion can be a meaningful warning signal, regardless of whether data copying actually happened later.
5. Use authorized-media records and real verification to make sure the policy truly works
After policy delivery, it is advisable to test one ordinary USB drive and one authorized drive on a controlled endpoint to confirm that the ordinary device is restricted while the authorized one behaves as expected. If the enterprise has stronger requirements around media ownership and lifecycle, it should also maintain an authorized-drive register with authorization time, purpose, holder, and change history, and remove authorization promptly when a device is retired, lost, or no longer needed.
Without this verification and ongoing register maintenance, USB governance can easily fall back into a “configured once, never checked again” pattern. In external device management, continuous maintenance matters more than one-time setup.
The value of Ping32
Ping32 does not just answer whether USB can be disabled. It provides a full chain for external storage governance. Permission Settings create the baseline of default control. Create Authorized Drive gives compliant media a clear identity. Approval workflows absorb business exceptions. USB Usage Alert gives administrators immediate visibility into abnormal insertion attempts.
That means enterprises no longer need to think about USB ports as a binary choice between fully open and completely blocked. They can keep unauthorized devices outside the endpoint while preserving approved devices and approved usage inside one manageable control framework. For organizations that need both security and business continuity, that is a far more practical model.
FAQ
Q1: If unauthorized USB devices are blocked, does that mean the company can no longer use USB drives at all?
No. A more practical approach is to block general USB devices while allowing only authorized drives, and to provide approval workflows for temporary needs. That allows legitimate business usage to continue without leaving the endpoint open to uncontrolled media.
Q2: Why is USB auditing alone not enough?
Because auditing mainly shows what happened after the fact. It does not decide in advance what is allowed to connect. If ordinary USB devices are still freely usable, then even perfect records do not change the fact that the endpoint boundary remains open. The baseline must be controlled first.
Q3: Once an authorized drive is created, is it permanently valid?
No. The manual explicitly notes that formatting an authorized drive cancels its authorization. In addition, loss, employee departure, and project closure should all trigger authorization recovery. Authorized drives should therefore be treated as a continuously maintained controlled list, not a static whitelist left untouched over time.












 Contact
Contact

































 9 min
9 min