Printing is one of the most underestimated channels in enterprise data leakage. Screens can be watched for screen recording, peripherals can be locked down at the port level, and outbound network traffic can be inspected by content engines. But once a file enters the print queue and lands on physical paper, the digital security perimeter simply ends. A contract marked as confidential, an unannounced financial report, a snippet of research and development source code — a single click on Print is often enough to bypass most electronic controls and quietly walk out of the company.
What makes the problem worse is that printing is perceived as ordinary. Whether employees are printing a contract, a name list, or an attachment from an internal email, very few of them pause to consider that the document in their hand may contain sensitive data. From a management perspective, the real challenge is never “did a print happen” but “who printed which document at what time, how many pages came out, which printer was used, and whether the behavior is high risk.” In many organizations these questions cannot be answered reliably after the fact, leaving investigators with only subjective judgment and patchy paper records.
Why Paper Leaks Remain the Hardest Channel to Seal
When you break the problem down, print auditing is difficult along three distinct axes. The first is the fragmentation of behavior itself. A print job may originate from Word, from a PDF reader, from a browser print preview, from an ERP client, or from any line of business system that embeds printing. Outputs fan out to local printers, network printers, virtual printers, and shared printers. A missing collection standard on any one path turns into a blank spot in the audit chain.
The second axis is the invisibility of content. Traditional print logs can tell an administrator that “an employee printed N pages at a particular time,” but they cannot reconstruct what was actually on those pages. When a suspected paper leak surfaces, an organization without a content snapshot has no reliable way to tie a physical sheet back to a specific print job, and therefore no way to close the evidentiary loop.
The third axis is the lack of deterrence. Even when print logs exist, if employees do not know that their print activity is being recorded, and if the printed output carries no visible traceability mark, then at the critical moment of deciding whether to print a sensitive document and carry it off the premises, the audit system exerts no real pressure. Effective governance requires three layers stacked together: deterrence before the act, interception during the act, and evidence after the act.
Auditing and Watermarking: Two Sides of the Same Problem
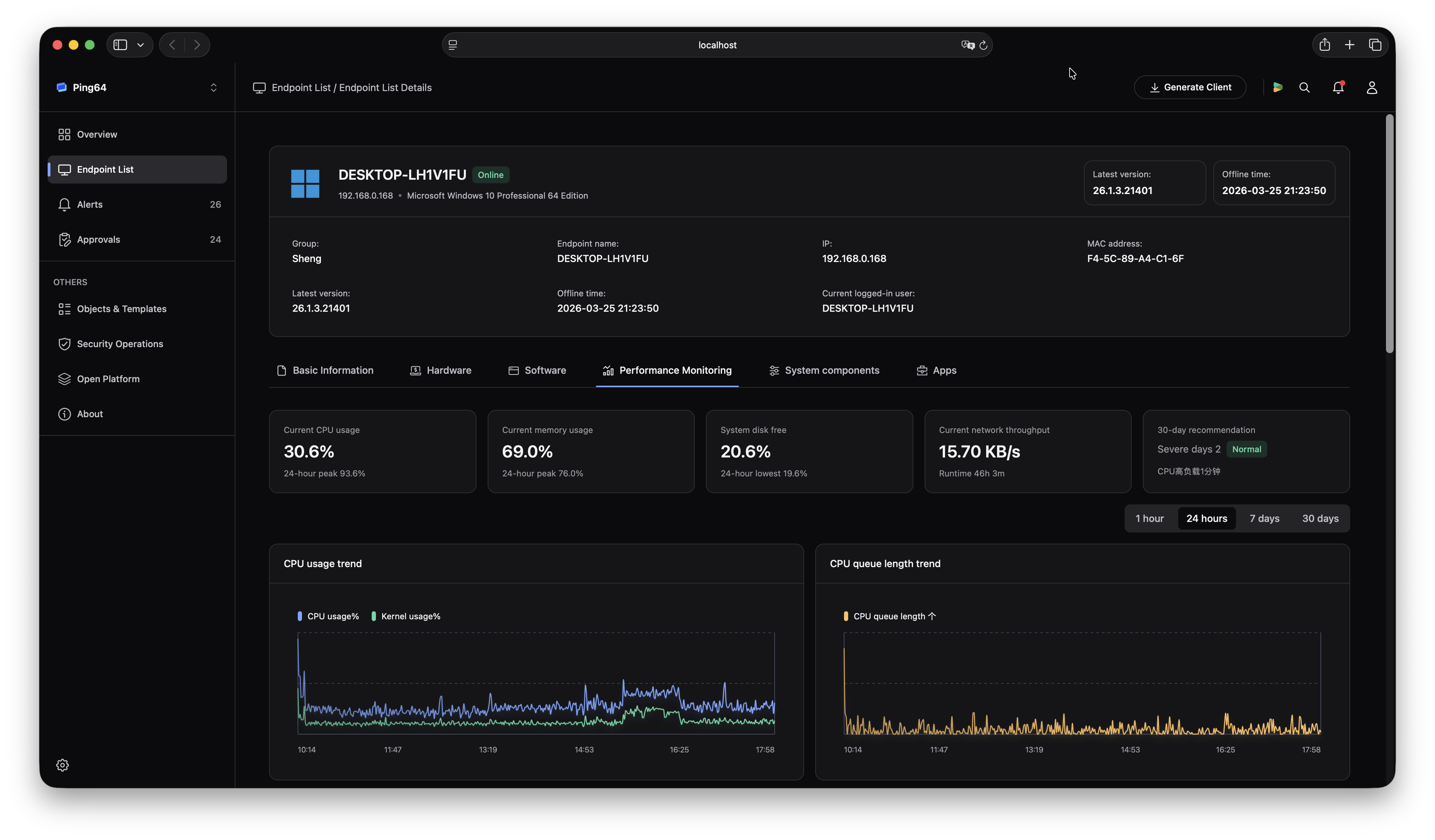
To make print governance credible, two questions must be answered at the same time: what was printed, and can the physical sheet be identified later. The first question corresponds to print auditing, which requires administrators to see who printed, on which endpoint, using which printer, which document was targeted, how many pages were produced, and at what time — and to be able to review page thumbnails and original images of the printed content when necessary. The second question corresponds to print watermarks, which requires every printed page to carry an identifying mark — an employee name, a machine name, a department name, a MAC address, a date and time, or some combination — so that a sheet of paper can be traced back to its origin once it leaves the office.
This is why Ping64 places print auditing and watermark policy inside the same governance frame within its data loss prevention module. On one side, Ping64 collects the complete metadata of every print job from the endpoint and returns the original pages as images to the management console, forming a traceable print auditing view. On the other side, Ping64 manages screen watermark, window watermark, URL watermark, print watermark, and file watermark as five sub-policies inside a single watermark policy entry, so administrators never have to switch between modules to cover every egress path with watermarking. For the enterprise, the value of this design is simple: you look at one view when you are hunting evidence, and you use one entry when you are pushing policy, and the link between the two never breaks because of a module switch.
Closing the Print Governance Loop in Ping64
The following is a practical sequence you can run inside the Ping64 console. Administrators should complete the steps in order; skipping a section leaves the deployment with either audit visibility but no deterrence, or watermarks but no evidence.
The first step is to open the Print Auditing page under the data loss prevention module. This page is Ping64’s unified view of printing behavior across the organization. The top of the page offers advanced filters on five dimensions — department, user, operator account, printer name, and print title — while the upper right hosts the date range picker and the export button. Start by setting the range to the most recent thirty days and scan the default sort order for the overall print volume distribution, printer concentration, and any outlier where a single user shows an unusually high number of printed pages in a short window. The scope of this step is every endpoint that has the client installed, and the way to verify it is to print a test document from any managed endpoint, return to the Ping64 print auditing list and refresh — you should see the corresponding department, user, printer name, print title, page count, and date fully populated in the table.
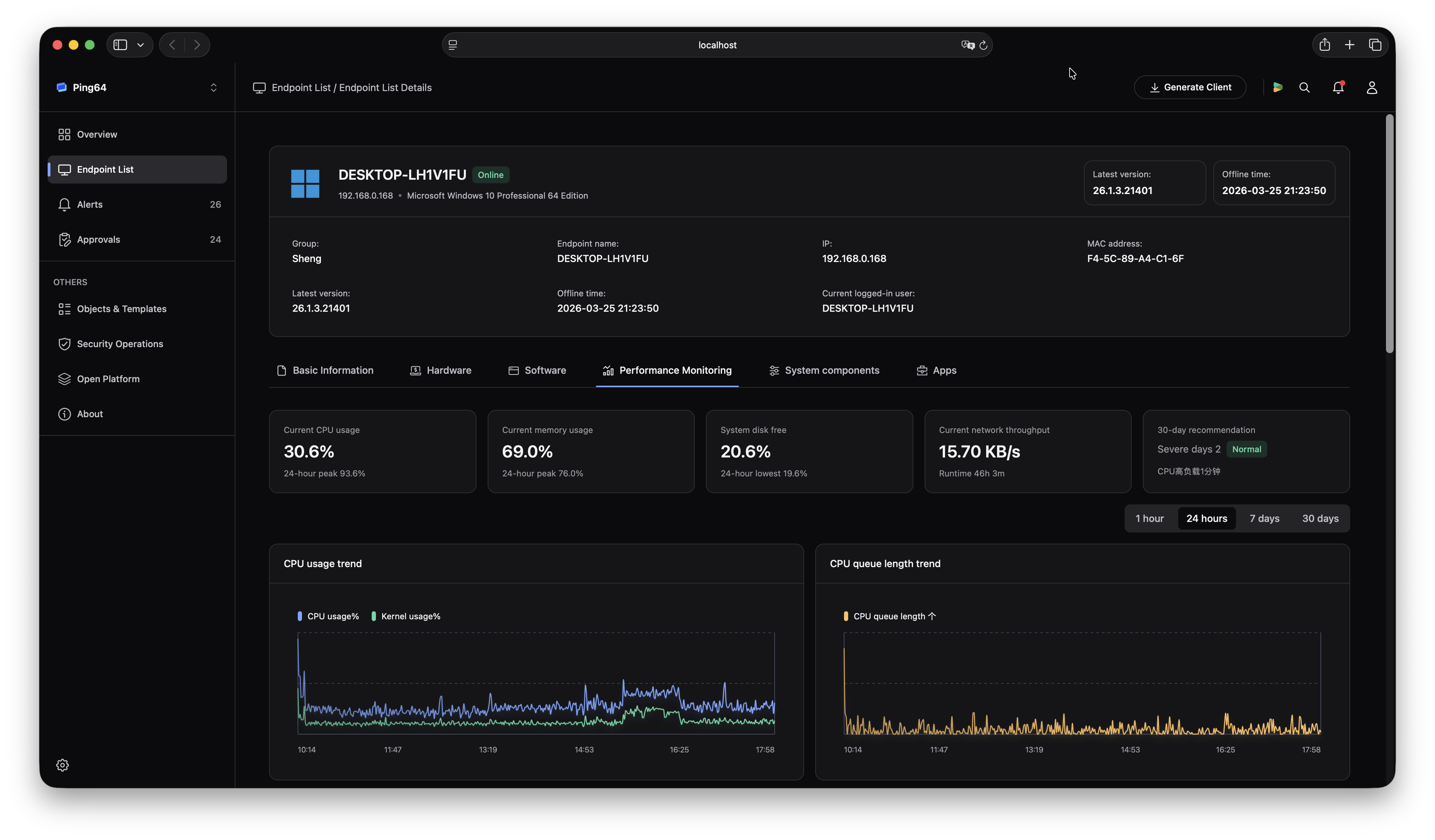
The second step is to click any record to enter the print auditing detail page. A Ping64 detail page is laid out in three regions: a header with basic information, page-level thumbnails, and a preview toolbar. Clicking any thumbnail expands a high resolution preview, and the toolbar offers zoom in, zoom out, rotate left, rotate right, download, and print actions in that order. Use this page to check whether the content on the paper matches the document title in the audit record, and whether an employee may have deliberately changed a document title to evade auditing. Ping64 decompresses and presents every page in order, so you will not miss pages during evidence collection. The scope here is a single print job, and the way to verify it is to pick a known sensitive document record, preview every page, download an original image of one page, and compare it against the actual printed sheet — the contents should match exactly.
The third step is to move into the data loss prevention policy module and open the watermark policy card. Inside Ping64, watermark policy is defined as a single configuration that contains the five sub-policies for screen, window, URL, print, and file watermarks. Switch the left-hand tab to Print Watermark, turn on the enable switch for that sub-policy, and select an existing template from the print watermark template dropdown. If no suitable template exists yet, go to watermark template management first and create one, including traceable fields such as employee name, machine name, department, and date and time, placing the mark above or below the text and choosing a display style such as tile, center, top right, or bottom right. The scope is every online endpoint covered by the policy, and the way to verify it is to save the policy, reprint a document from a test endpoint that has received the rollout, and confirm that every printed page carries the configured watermark content in the selected position and style.
The fourth step is to attach an approval flow to the print watermark inside the same watermark policy. By design, every print output under the policy in Ping64 carries the print watermark. In practice, however, there are legitimate scenarios — external deliverables, bid documents, legal archives — where a watermark-free physical copy must be produced. Under the print watermark sub-policy, select an approval flow so that employees can request to remove the print watermark for specific business cases. Ping64 standardizes the corresponding approval action, so administrators do not need to stitch it together themselves. The scope is the subset of business users who need exception access, and the way to verify it is to submit a remove-print-watermark request from a regular account covered by the policy, reprint during the approved window after the request is granted to confirm that the paper comes out clean, and then reprint again after the approval expires or is rejected to confirm that the watermark is automatically restored.
The fifth step is to return to the print auditing page for a final end-to-end check. Open the advanced filter, search for the department or user name of the account used for the test, limit the time dimension to today, and you should see the audit record that corresponds to the test print job, with a page count that matches the physical sheet. When you enter the detail page, the watermark content should also be visible on the thumbnails. This cross check matters because it simultaneously proves two things: print auditing is not dropping events, and the print watermark policy is in fact applied on the real output path.
Beyond these five steps, there are three boundary cases worth calling out. First, virtual printers. Some employees habitually print to PDF first and then forward the file; Ping64 still records that behavior as a print job in the print auditing page, and the printer name field reflects the corresponding virtual printer. Administrators should not dismiss these records just because no physical paper was produced. Second, client version lag. Print watermarking depends on client-side overlay, so a newly pushed policy only takes full effect after the client has been upgraded to a version that supports the relevant sub-policy. On first rollout, validate in a test group before expanding to the full fleet. Third, audit trails during an approved window. Even when the watermark is temporarily removed, Ping64 print auditing continues to record the full metadata and page thumbnails of that print job. This is a compliance-grade safety net, and administrators do not need to configure it separately.
From a Single Click to a Traceable Paper Archive
Closing the loop on printing is really about turning a single click into a traceable archive. The print auditing capability that Ping64 provides keeps every paper output accountable in the back office. The print watermark capability that Ping64 provides gives every sheet that leaves the building an identifying mark. And the approval flow inside Ping64 keeps the whole mechanism flexible enough not to block legitimate business. Together, these three capabilities let an enterprise project a visible deterrent — print and you leave a trace, print and you carry a mark — exercise sensible exceptions through policy and approval during operations, and reconstruct the chain of responsibility afterward through audit detail and watermark forensics. For administrators, printing is no longer a black box action but a visible line that runs from click to policy filtering, to watermark overlay, to audit archiving. This is why a growing number of security teams now include the Ping64 print auditing view in their daily inspection routine and treat the Ping64 watermark policy as a compliance baseline item. On the last mile of data governance, the ability to bring paper risk back into the system’s field of view is itself a core component of enterprise data asset protection.












 Contact
Contact

































 10 min
10 min