Printed output is still one of the easiest data leakage paths for enterprises to overlook. Digital files may already be protected by permissions, logging, and encryption, but once they are turned into paper, the range of distribution, the number of copies, and the path of physical circulation become much harder to trace. For financial reports, customer lists, draft contracts, engineering drawings, and HR records, the real question is not simply whether printing should be allowed. It is whether the organization can decide which endpoints may print, which content must be blocked, which exceptions require approval, and whether evidence remains available afterward.
Many printing risks are not caused by obviously malicious behavior. They happen in normal workflows: an employee prints an unfinished document for a meeting, a contractor prints a client list before leaving site, or a team repeatedly copies a document that contains confidential fields. If those actions are governed only by policy documents and not by endpoint controls, enforcement quickly becomes inconsistent. A practical governance model usually requires printing permissions, printing audit, print watermarking, and exception approval to work together.
Why printing often becomes a blind spot in data protection
Printing does not depend on a network channel, does not pass through an email gateway, and does not naturally leave a complete transmission trail. Many enterprises already monitor file transfers, USB copying, and messaging-based sharing, yet paper output remains weakly controlled. Once endpoints are free to print, high-value information can be converted into paper and leave the managed environment without any meaningful warning.
Another challenge is that many roles do have legitimate printing needs. An organization cannot rely on manual judgment for every print job forever. The realistic answer is not to allow everything, and it is not always to block everything either. What works better is layered control: restrict by default, identify by content, release exceptions through approval, and preserve traceability through audit. Without that structure, printing control tends to become either too disruptive or too weak to matter.
Common execution problems enterprises face in print governance
The first problem is unclear scope. Many teams know printing is risky, but they struggle to define which departments should be fully blocked, which should only be restricted for sensitive content, and which roles need temporary exceptions. Without grouping by endpoint, role, and business scenario, policies usually become either too strict or too loose.
The second problem is the absence of evidence. Even if a company later discovers that a document has leaked, it may still be unable to answer basic questions: who printed it, when it was printed, what was printed, and whether a backup of the print content exists for review. If a system only blocks actions and does not preserve logs, investigations still fall back to manual guesswork.
The third problem is traceability after the document leaves the system. If printing is allowed, the paper output should still carry some accountability. Print watermarks do not replace access control, but they do improve attribution if a printed document is copied, photographed, or redistributed later.
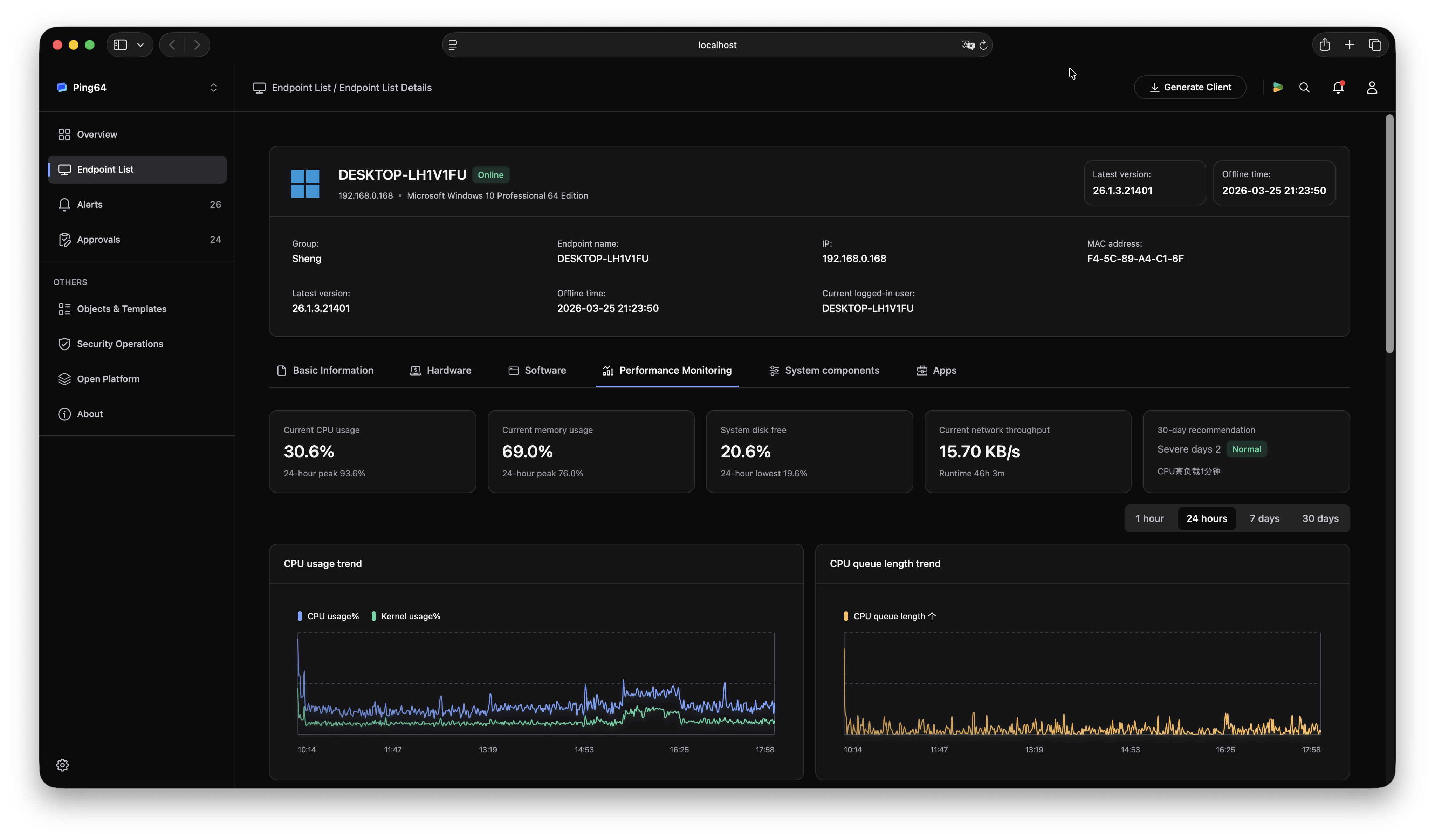
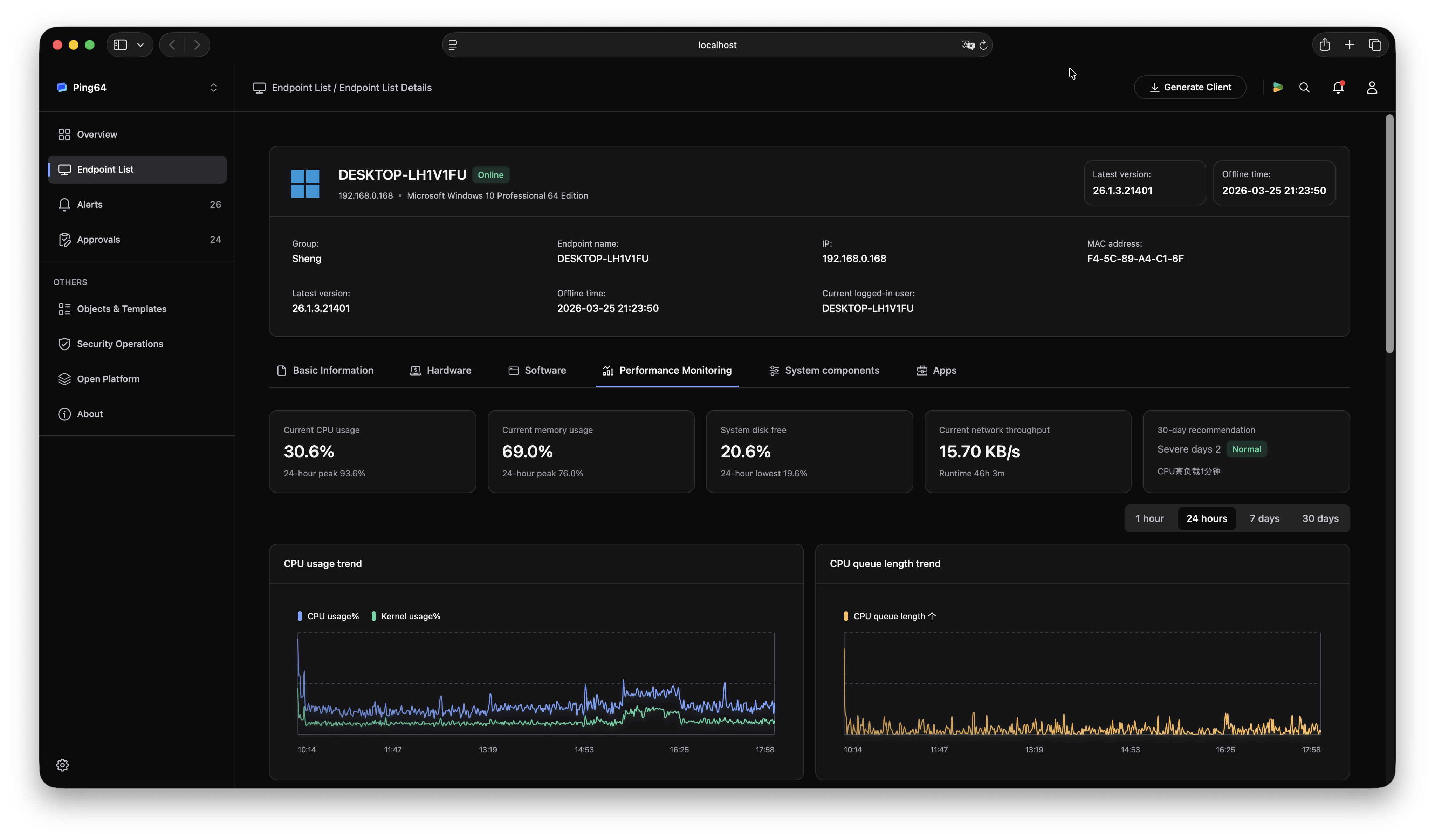
How to use Ping32 to control printing and retain audit evidence
1. Enable print control in policy and choose the control model
In the Ping32 console, an administrator can open Data Security -> Policy -> Print Security and enable Print Control. In parameter settings, the policy can be configured to Block printing of all files, Block printing of files containing sensitive words, or Allow endpoints to submit print requests. If the immediate goal is to close the print exit quickly, a default deny model is appropriate. If the organization still needs day-to-day flexibility, content-based blocking with approval-driven exceptions is usually a better fit.
2. Configure print approval for roles that need exceptions
When some departments still need temporary print access, the same print control policy can enable Allow endpoints to submit print requests and bind it to an approval workflow. After the policy is applied, users can submit a print request from the client, including a title, description, printer, print task scope, and valid time window. This prevents the business from weakening the entire control model just to accommodate a small number of legitimate exceptions.
3. Enable print log audit and back up printed files when needed
To make printing governance traceable instead of purely restrictive, administrators can also enable Print Log Audit under Data Security -> Policy -> Print Security. If the enterprise needs stronger evidence retention, it can additionally enable Back up printed files. After policy deployment, print records can be reviewed in Data Security -> Print Audit, where the team can verify print time, print target, and related audit details.
4. Add print watermarking when paper traceability matters
For contracts, lists, drawings, internal reports, and other highly sensitive material, the enterprise can further enable Print Watermark in Data Security -> Policy -> Print Security and choose an existing print watermark template. This helps ensure that even after the document leaves the endpoint environment, the printed page still carries identity markers, timestamps, or tracking fields.
5. Verify that blocking, approval, audit, and watermarking work together
After policy rollout, it is worth validating at least four outcomes on a test endpoint: whether ordinary files are allowed or blocked as expected, whether sensitive content triggers restriction, whether approved print requests work within the allowed window, and whether the print audit view records the event correctly. If printed file backup or watermarking is enabled, those results should also be checked.
What practical value this brings to the enterprise
The main value of print security is not just reducing the number of print jobs. It is giving the organization a way to manage paper output with rules and evidence. Many enterprises have invested in protecting digital data, yet still leave a clear gap at the point where data becomes physical. By combining print control, approval, and audit in one model, Ping32 helps bring paper output back into a visible and enforceable governance framework.
This approach is also more executable than relying on policy reminders alone. Instead of asking users to voluntarily avoid printing, endpoint policy defines what is allowed, what is blocked, what requires approval, and what will be recorded. That reduces the likelihood of high-risk print-based leakage while preserving limited flexibility for legitimate business needs.
FAQ
Q1: Does the enterprise need to block all printing from the start?
Not necessarily. High-sensitivity groups such as R&D, finance, and HR may justify a default-deny approach, but general office scenarios can begin with sensitive-content blocking or approval-based exceptions and tighten later if needed.
Q2: What is the difference between print audit and print control?
Print control governs whether printing is allowed in the first place. Print audit records who printed what and when, so the organization can investigate later. They solve different problems and are strongest when used together.
Q3: Can print watermarking replace print access control?
No. Print watermarking improves accountability and traceability, but it does not replace access control. For high-risk documents, print control, print audit, and print watermarking should be combined rather than used in isolation.












 Contact
Contact

































 7 min
7 min